Storage-Aware SOAR Playbooks: Turning Incident Response Into Deterministic Data Protection
- Date: Feb 27, 2026
- Read time: 4 minutes
Modern ransomware response cannot stop at the endpoint.
Attacks ultimately manifest at the data layer — through file modifications, encryption, deletion, and exfiltration.
Traditional SOAR platforms orchestrate alerts across identity, endpoint, and network tools. But without storage-aware enforcement, containment remains incomplete.
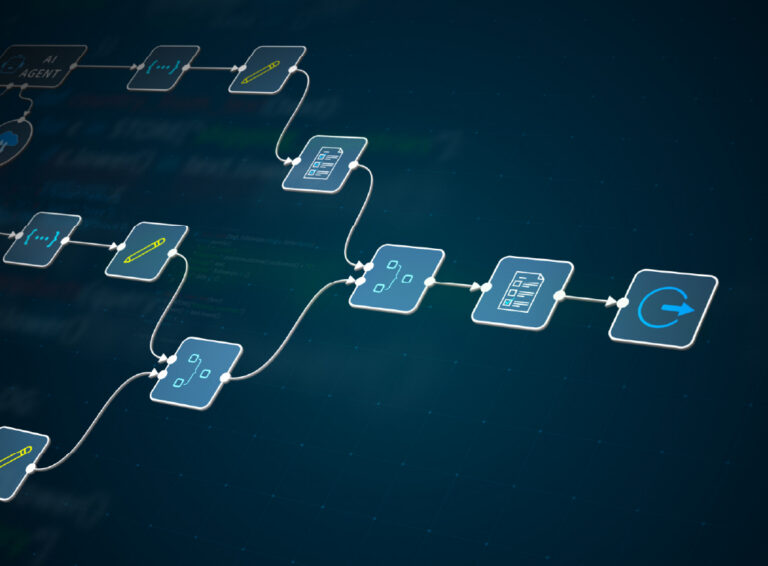
Superna extends SOAR into the storage tier — enabling deterministic actions such as:
· Immediate user lockout from NAS data
· Host-level storage access revocation
· Immutable snapshot creation
· Data access anomaly scoring
· Data attack surface risk queries
· Session termination
· Endpoint isolation orchestration
This is Cyber Storage Incident Response — storage-enforced automation embedded directly into existing IR workflows.
Playbook #1 — Compromised Credentials / Phished User Account
Trigger
· Confirmed phishing incident
· Suspicious login behavior
· MFA bypass alert
· Credential abuse detection
· High-risk IAM classification
The Traditional Gap
· Disabling AD does not invalidate active Kerberos sessions
· Endpoint isolation does not prevent credential reuse
· Data remains accessible during the session window
Storage-Aware SOAR Action
· Revoke user SMB/NFS data access immediately
· Terminate active storage sessions
· Trigger immutable snapshot of impacted datasets
· Retrieve user accessible data summary and anomaly score
Outcome
· Active sessions destroyed in real time
· Data exfiltration or encryption halted
· Clean recovery point preserved
Playbook #2 — Bulk Phishing Campaign / Early Ransomware Spread
Trigger
· Email gateway flags phishing wave
· Multiple suspicious email reports
· Endpoint infection confirmed
· High-severity SOC escalation
The Traditional Gap
· Protection is reactive
· No proactive data-layer protection
· Encryption may begin before containment completes
Storage-Aware SOAR Action
· Create immutable snapshots for critical datasets
· Identify high-value users accessing sensitive data
· Temporarily revoke storage access for high-risk accounts
· Trigger endpoint isolation and deep scan
Outcome
· Immediate recovery checkpoint established
· Blast radius reduced before encryption spreads
· High-value data proactively protected
Playbook #3 — Employee Termination / Insider Risk
Trigger
· HR termination workflow initiated
· Privileged or high-risk employee flagged
· Sensitive data access present
The Traditional Gap
· User may still be logged in
· AD disablement does not terminate active sessions
· Malicious deletion or copying can occur pre-exit
Storage-Aware SOAR Action
· Revoke storage access immediately
· Terminate active data sessions
· Create protective immutable snapshot
· Generate 30-day user data access report
Outcome
· Prevents malicious delete or copy activity
· Preserves restore point if tampering occurs
· Provides forensic audit trail
Playbook #4 — Active Ransomware / Destructive File Behavior
Trigger
· Mass file renames detected
· High-entropy write bursts
· Accelerated modification rates
· Unusual delete behavior
· Endpoint detects ransomware process
The Traditional Gap
· Alerting without deterministic containment
· Delayed storage protection
· Incomplete recovery assurance
Storage-Aware SOAR Action
· Block host storage access
· Block associated user access
· Trigger immediate immutable snapshot
· Initiate endpoint isolation and deep scan
· Enrich incident with file list and risk score
Outcome
· Encryption halted at storage layer
· Clean recovery preserved
· Full forensic context available immediately
Playbook #5 — External Network Penetration / Elevated Threat Posture
Trigger
· IDS detects brute-force attempts
· Firewall intrusion alerts
· Heightened threat posture declared
· Active DOS or penetration event
The Traditional Gap
· Monitoring only
· No proactive data protection
· Recovery posture not validated
Storage-Aware SOAR Action
· Accelerate snapshot cadence
· Execute AirGap vault job for recent data
· Query host data attack surface risk
· Increase behavioral monitoring sensitivity
Outcome
· Multiple recovery checkpoints created
· Vault posture validated
· Data recoverability ensured even if breach succeeds
Built for Orchestration
Superna integrates with over 35 vendors across more than 60 integrations, embedding storage-aware controls directly into SIEM, SOAR, endpoint, identity, and ITSM platforms.
Conclusion: Storage-Aware SOAR Is Level 3 Incident Response
Mature incident response requires automated containment, deterministic enforcement, root-cause visibility, and clean recovery assurance.
By embedding storage intelligence directly into SOAR workflows, organizations move from reactive investigation to orchestrated remediation.
Ransomware impacts data. Your response should protect it.
Featured Resources

Mastering Cybersecurity Insurance Negotiations: A Comprehensive Guide
Navigating the Digital Menace: A Beginner’s Guide to Ransomware

